Hello All,
I've read through most all posts in this board relevant to OAuth ~/restapi/oauth/authorize and ~/restapi/oauth/token Authentication methods.
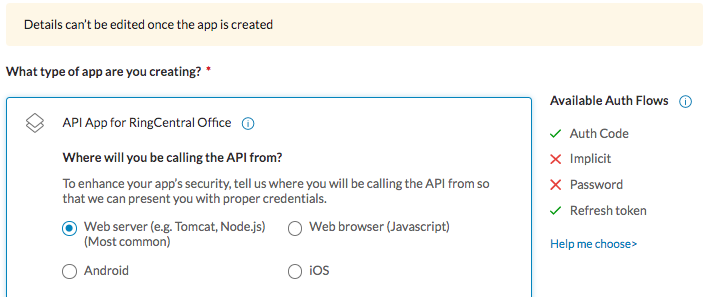
My use-case is germane to AppType Webserver and Other Non-UI. Generally speaking, our code (that engages the RingAPIs) may be triggered by various events. None of these have a Ring User context which is required to support grant_type=password.
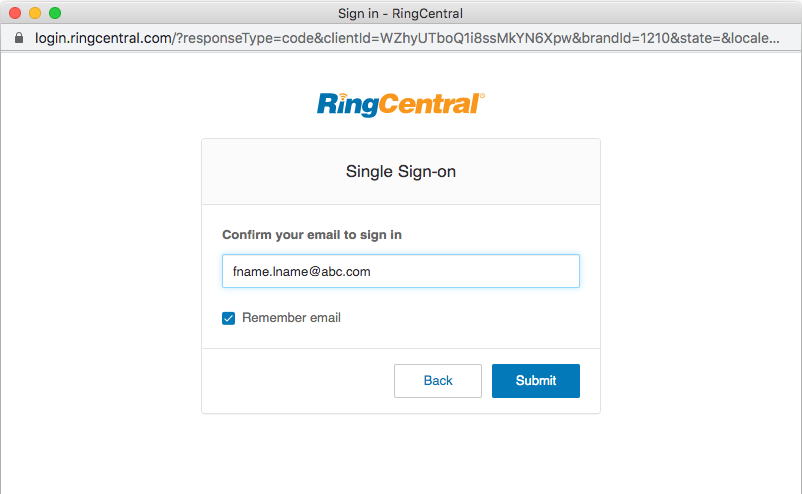
The primary constraint we have, any OAuth grant_type method that requires Ring User/login ID/PWD/Ext/Phone# does not work when SSO is enabled for user logins. This means we can only use grant_type=authorization_code.
For us, auth_code means a SAML Assertion. It also means a Ring User/login is required, and we're back to - there is no Ring User context, only the registered Ring App context.
The example shown in Authentication Your Application - Is the in-body grant_type=password(+credentials) actually required?
If not, that example should work perfectly - but it doesn't. Are we missing something?
Microsoft provides a detailed how-to for this use-case, appropriately named "Get access without a user" :)